Hey all,
For the next few weeks we’re shifting the format from doing liveshares on vulnerable machines to doing a more conventional class structure supported by instruction, followed by lab time.
Much of the instruction is being done by an OSCP / OSCE holder as well as a regular speaker, most recently at BSidesLV and Defcon25.
I’m currently in the process of building a vulnerable network which mirrors boxes found in the OSCP labs which should be done by the next meeting.
If you want to catch up go through weeks 1-2 on:
https://pentesterlab.com/bootcamp
Thanks!
– Flay
POST MEETING MINUTES 8/25/17:
- cmdandcontrol did a live walkthrough of weeks 1&2 from pentesterlab (including writing the http clients).
- httplov3craft shared A sick method for Bypassing Split-Token UAC on administrative accounts. This is current for fully patched and updated windows 10 as of 8/26/2017.
- flay shared an enhanced interpreter called
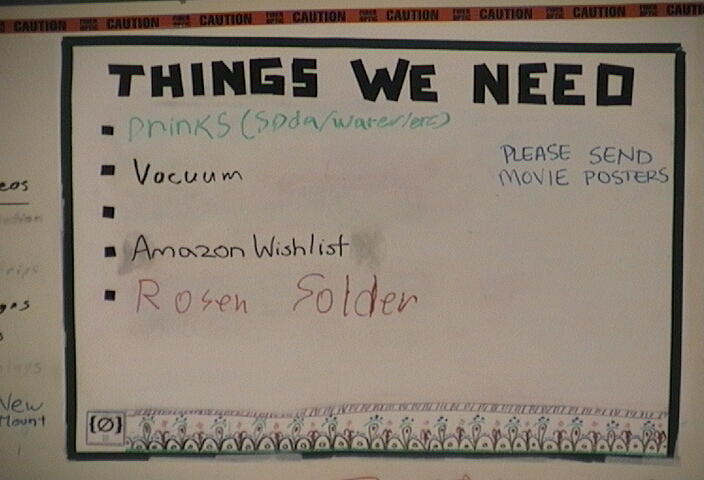
bpythonand showed how it can be used to do speed up python script development. Its awesome, you should use it. - meatbunny and f13 threw in serious work in getting the infrastructure ready for the oscp simulated lab. I stayed through most of the night and got 8/10 of the vulnerable machines live, so as of now it is ready to use.
- NEXT WEEK: Weeks 3 & 4 on ptl-ptl-bootcamp Read up on PHP & DNS as well as SSL / TLS and do the exercises.

Leave a Reply